What does work/life balance mean to you? Most likely, it means something different to what it means to me.
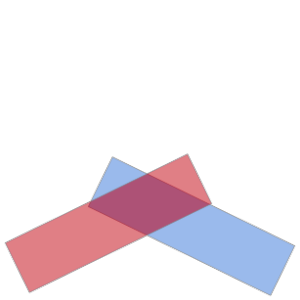
There are many ways to define work and life, and the balance between
the two, but I’m going to focus on two, that I’ll label, ungenerously to
one of them, the “old way” and the “new way”.
The old way
In the old way, work and life are clearly distinct, as night and day.
Work is a curse (sometimes biblical), the time you spend toiling and
sweating and bleeding to earn a living, and life is a blessing, the
thing you work for, which must be distinct from work and much better
than work, to justify all the toiling and sweating and bleeding.
You work (an activity that by definition you do
not enjoy most of the time) to earn money, that you then spend on things that you
do
enjoy, during your “life” time. The work is an unfortunate necessity,
something that you would avoid if you could. The ideal life is the
infinite holiday. If you had millions of dollars instead of
thousands, in this mental framework, you would probably go on an
extended holiday, until you’re either ruined by unfortunate
circumstances or you die.
This is still the dominant paradigm, and one that drives most of our
discussions of work/life balance. In fact, the very term “work/life
balance” implies belief in this old way of defining work and life.
Whenever you say “work/life balance”, you imply to your subconscious
that you believe in these two concepts of work and life and their
contrast and the need to balance them.
How to balance them? Well, with the definition of work as something
unpleasant and life as something pleasant, obviously work should be
minimised and life maximised. So we have fixed working hours, 40 hours a
week, then 35, then 30. We scrupulously “leave our work behind” when
we go home. We take holidays where we make sure to disconnect. We look
at people who work longer hours, take their work home and work on
holiday as workaholics – a clearly, obviously pejorative term. Something
to be avoided.
The new way
The new way of talking about work and life is from the point of view
of passionate people doing work they care about deeply. The traditional
view here is that only artists and vocational people like charity
workers, priests or doctors can do that, but today’s reality is that
many people engaged in a wide range of jobs can and do feel passionate
about their work, and find personal accomplishment and fulfilment in
them.
One obvious case of the passionate worker is the entrepreneur,
but they are rare so let’s leave them aside. Another is people who work
in open cultures, or at least in jobs that somehow have some mysterious characteristics like a
sense of purpose and challenge and autonomy.
People in these kinds of jobs can frequently feel they are in an
awkward place, because they feel that they enjoy working hard, but then
the “old way” of thinking tells them that they’re working
too hard. Adopting
the language of the old way, they might end up “realising” that they’re
workaholics and try to cut back, or go on holiday and deliberately
disconnect from everything to try and recover some “work/life balance”.
The sad thing about this is that it is wrong and actually makes the
passionate person’s life worse, not better. Being passionate about your
work is not a curse, it’s a blessing. We can argue all year long about
what the meaning of life is, and each person can and needs to come up
with their own answer, but there is no argument that achieving a
state of flow is a desirable thing. Being passionate about your work leads to being in a state of flow more often.
How tragic, then, when definitions imagined by people who worked in a
state of pain rise up out of your subconscious to say, effectively,
“hey, you shouldn’t spend that much time in a state of flow, you’re a
workaholic with no work/life balance!” An exaggerated view of that is
akin to interrupting Leonardo in the middle of painting the Mona Lisa to
tell him he’s done his eight hours and needs to go home now.
This conflict between working according to the new way but letting
your thinking err along the old way is not helpful, and in my opinion
should be avoided. I propose a new way of thinking about work/life
balance, in terms of stages of work, with a clear, opinionated scale
from worse to better. Each stage has different ways of thinking about
work/life balance.
The new ladder of work
Level 1: Slavery
Level 1 – Slavery
On the bottom of the ladder, I would like to put slavery – by which I
do not mean wage slavery, but actual, real slavery. There is still an
awful lot of this in the world. Some countries still have
institutionalised slavery, and some
high-profile international organisations do not bat an eyelid at using slavery to
serve their goals, and most of humanity through most of history has
operated at this level, sadly. As a slave with no control over your
life, we can perhaps miraculously lift ourselves up to a higher level
(like Joseph in the Biblical story), but most, by far, will not. The
concept of work/life balance is irrelevant here: we have no life as a
slave, our life belongs to our master.
Level 2: Survival
Level 2 – Survival
One level above, I would put the type of work that one does to ensure
survival (of oneself or of one’s family). Throughout the industrial
revolution, and still in many countries in Asia in industries such as
textiles or manufacturing, much of the work is at this level. This is
barely above slavery, the only difference being that we have a notional
choice of working under equally bad conditions somewhere else. Work/life
balance as a concept becomes theoretically important but is mostly out
of our reach. We work (serve the curse) as much as we humanly can, and
the rest of the time is a temporary interval between stretches of work.
Much of the social progress of the industrial revolution was aimed at
allowing people working at this level to live humane lives, and lifted
much of the western world’s population to at least level 3.
Level 3: Balance
Level 3 – Balance
This is the level where the concept of work/life balance really has
full meaning, and where most people are operating. In this perspective,
work is undesirable but not oppressive. We have choice, so long as the
economy is doing alright and our skills are in demand. We can choose to
work reasonable working hours. We have control over the line between
work and life. This is the old way done right. In this context, the
concept of work/life balance is a good thing and it is important to
balance the two, to stay in control of where that line shifts.
Level 4: Acceleration
Level 4 – Acceleration
Some fortunate people operating at level 3 may find that some aspects
of their jobs are more engaging than others, and get caught up in those
aspects from time to time. Another way to put it is that we may have
work that is largely undesirable, that would not be worth doing if we
weren’t paid for it, but there are some aspects of that work that put us
in a state of flow, where we lose track of time and find ourselves
working till silly hours or thinking about work on holiday, etc. This is
where the level 3 way of thinking holds us back, by suggesting that
this is a symptom of an out of control work/life balance. At this stage,
the concept of work/life balance still makes sense overall, but it
starts to lose its usefulness, and I think this is the stage where we
must be careful not to let it hold us back from progressing to level 5.
Because at level 4, we start to get a glimpse of what life could be
at level 5, since we begin to find out which activities are both
productive (i.e. things society rewards with money) and put us in a
state of flow (i.e. things we deeply enjoy doing for their own sake).
Level 5: Flow
Level 5 – Flow
Once we discover which activities we can do, which put us in a state
of flow but are rewarded by society (i.e. are paid well enough),
we have the option to start rebuilding our work (or finding another job
or career) where we can spend most of our time doing the things we love
and are passionate about. Of course, there are always going to be some
unpleasant bits to any job, but because we see the bigger picture of
what we’re doing (flow is impossible without a sense of purpose),
we handle them without much effort, to get back to the bits we enjoy.
At this level, work/life balance makes no sense whatsoever. You
wouldn’t put a time limit on flow any more than you’d put a time limit
on any other enjoyable activity. Keep doing it as long as it’s fun! When
it’s no longer fun, switch to another fun and productive thing. And so
on, endlessly.
I don’t think it is possible to reach this level without letting go
of the concept of work opposed to life, prevalent in level 3 thinking. A
career/life where you spend most of your time in a state of flow is
highly desirable, but it is not one we can reach while we meter out our
efforts and keep thinking of work as something to be avoided.
A symptom of this state, in my opinion, is that we are constantly
working: at home, during hobbies, on holiday, even while asleep!
But much of that work is subconscious, thinking about how to do things
even better or which things to do, rather than sitting down in front of a
computer and “working”. The work is then just the natural outlet of the
thinking, much like an artist’s work.
Whilst the shift from level 3 to 4 can happen accidentally without
intention, the shift to level 5 only occurs if we really seek out this
new way of working, which is why it’s important to embrace it rather
than fight it.
Some final notes
There are a million objections to the ideas above. Some obvious ones
are “what about if I have children?” or “what if my job sucks? no one
could possibly enjoy my job!”. I believe that a careful reading of the
article combined with some thinking will present answers to those
objections though. Have a think before you disagree.
In conclusion
Life and work need not and should not be in opposition. When they are
in harmony, both get better. But if you let the oppositional thinking
of work vs life drive your thinking, it will impair your ability to
progress from level 3 to level 5.
Don’t let old assumptions determine how you live your life today. Think for yourself about what makes sense for you.